There are two different sets of categories in cyber insurance: (1) First-party cover and third-party cover; and (2) stand-alone and packaged cyber insurance.
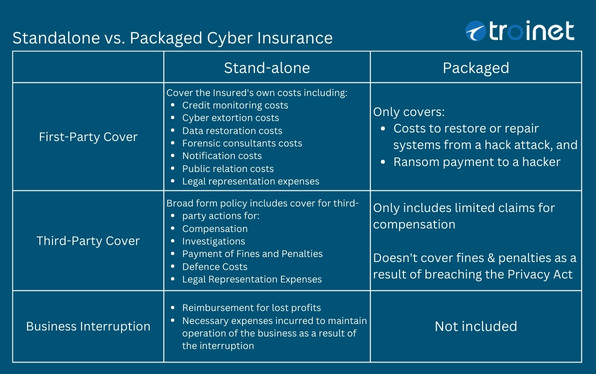
First-party cover
A more straightforward way to think of first-party coverage is, “If something happens to my business, this is what will be covered.” If cyber security risks materialize to you as the business owner, then these actions or costs will be shouldered by the insurer.
Third-party cover
Third-party coverage protects against a threat actor gaining access to your business, but they are only able to affect someone else’s information. In other words, they’re only able to attack someone else because they have breached your system. In such cases, the insurer accepts liability and undertakes these necessary steps at its own expense.
Business interruption
See “Why almost $3 Million data breach cost?”
Stand-alone vs. Packaged Cyber Insurance
A stand-alone cyber insurance policy covers all areas of cyber risk, whereas a packaged cyber insurance policy does not offer the full range of features.
There is a stand-alone cyber insurance product, as well as an option to purchase a packaged cyber insurance product. So if you have a commercial general insurance policy, there’s a way to add on a rider for cyber coverage. However, a rider typically only covers a few items, and its coverage can be limited in those areas, although it may also extend to other things.
In the cyber insurance industry, the most common cyber crimes that we see day in and day out are wire transfer fraud, annoying fake emails and texts, and phishing attempts.
This holds for both small- and large-scale events. These are the most common crime-related events, but unfortunately, these are typically not covered at all in packaged policies.
It’s wise to examine these stand-alone policies. Ensure that the coverage is comprehensive enough to protect against the most common cyber crimes.
“the most common cyber crimes that we see day in and day out are wire transfer fraud, annoying fake emails, and texts, and phishing attempts… unfortunately, these are typically not covered in packaged policies.”
Query: Are most people confused in thinking that if they have bundled or packaged insurance, they also have cybersecurity insurance?
Yes. That is spot on. Absolutely correct. That is a source of confusion for a good reason. They actually don’t have full cybersecurity insurance because they don’t have the full features that come with stand-alone cyber insurance.
They usually have a commercial policy, and they see an option to add on cyber coverage. If they are not reading through the details of the policy, someone might think, “Yeah, I already added cyber insurance.”
But it’s minimal when it’s a rider to a commercial policy. And that’s why it is so important to take the time to look at this, so everyone can understand what they have. Although it is still better than having nothing, a stand-alone policy will provide comprehensive coverage for all these threats, rather than relying on packaged or add-on riders.
It makes us nervous because people think they have cyber insurance, but it really only covers a small percentage of the threats out there.
Indeed, it is spot on to say that people are rightfully confused.
Cyber insurance has only been emerging for the last few years and is still not yet standardized as an insurance product; however, it is starting to become more standardized.
People are rightfully confused, and that’s why we seize these opportunities to provide as much education as possible.